ZynWork is designed as a secure system of record for project execution, financial tracking, resource planning, operational workflows, and related business records.
Our security approach is centered on practical control areas customers expect from a modern SaaS platform: tenant isolation, controlled internal access, secure authentication, encryption, backups, logging, change management, incident response, and transparent data handling.
Tenant isolation
Encryption in transit & at rest
Role-based access
Audit logging
Our approach centers on the control areas customers expect from a modern SaaS platform: tenant isolation, controlled internal access, secure authentication, encryption, backups, logging, change management, and incident response.
Data ownership first
Controlled provider access
Tenant-isolated design
Exportability
Security roadmap
Shared responsibility
Data classification and product risk profile
ZynWork is used to manage business-critical planning and execution data. Depending on customer usage, this may include:
For that reason, product security focuses on protecting confidentiality, integrity, availability, and controlled access across the lifecycle of customer data.

Data isolation and multi-tenant architecture
ZynWork follows a multi-tenant model with logical segregation of customer data.
Where feasible, new product features are designed with tenant boundary enforcement as a default requirement.
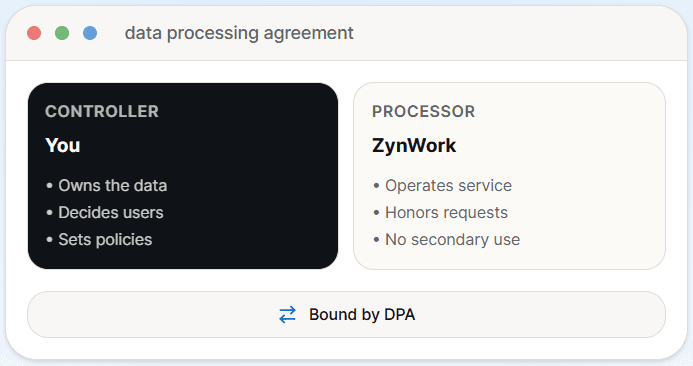
Data ownership, controller status, and processing role
Customers remain the Data Controller for the information they place into ZynWork. ZynWork acts as a Data Processor, handling data only for the purpose of delivering the service, support, maintenance, and related operational requirements.

Internal data access and transparency
ZynWork personnel may be able to access customer data under controlled and limited circumstances. This is disclosed clearly so customers understand the real operating model.
ZynWork does not access or use customer data for advertising or unrelated secondary purposes.
Authentication and access control

Encryption and data protection
ZynWork aims to protect data both in transit and at rest using industry-standard controls appropriate to the hosting environment.
Where specific encryption implementation details are required for a customer review, these are best confirmed against the live environment before being formally represented.
Application security and secure development
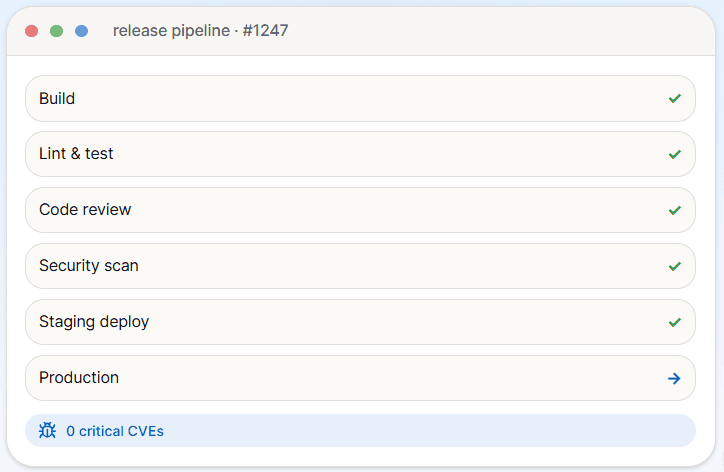
ZynWork aligns its application security thinking with generally accepted practices such as the OWASP Top 10, while avoiding claims of formal certification unless independently validated.
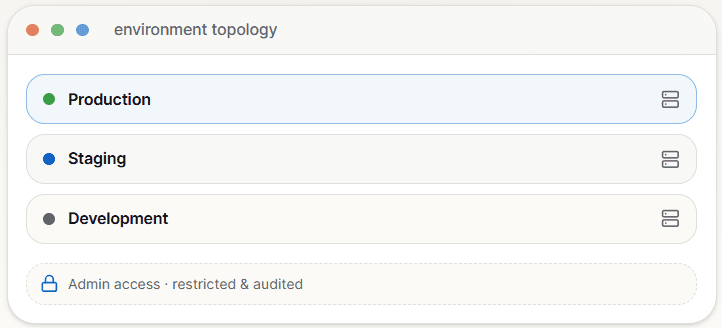
Infrastructure and environment security
Logging, monitoring, and auditability
Logging and monitoring are intended to improve reliability, support incident investigation, and provide an audit trail for privileged or support actions where available.
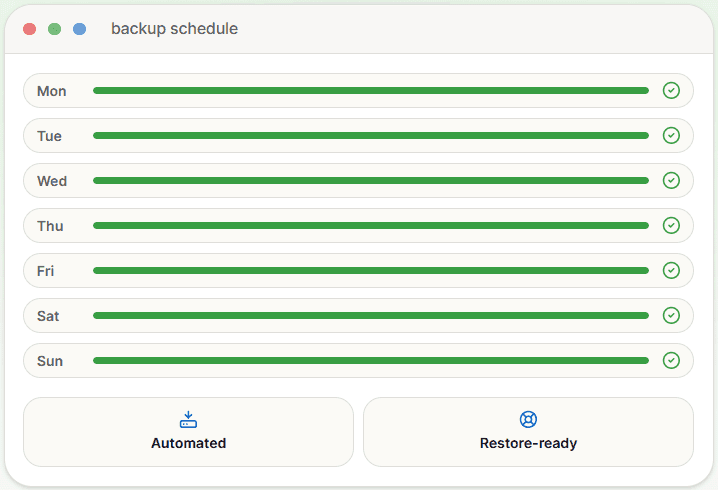
Backups, business continuity, and disaster recovery
ZynWork follows a multi-tenant model with logical segregation of customer data.
If customers require defined recovery objectives such as RPO or RTO, those should be documented separately in customer-facing commitments rather than implied on the public website.
Data retention, deletion, and export rights
ZynWork is intended to avoid unnecessary vendor lock-in by supporting reasonable data portability.

Incident response and security events
Vulnerability management and change control

Third-party vendors and subprocessors
Like most SaaS platforms, ZynWork may rely on third-party infrastructure, hosting, observability, communication, and development tooling providers.
Because vendor relationships can change over time, public website language should remain accurate at a category level unless a formal subprocessors list is maintained.
Privacy and confidentiality
Responsibility
CUSTOMER RESPONSIBILITIES
V/S

Compliance posture
Strengthening governance, on the road to SOC 2
ZynWork is strengthening its security and governance program over time, including documentation, traceability, operational controls, and audit readiness.
We do not represent ZynWork as SOC 2 certified today. The roadmap is real; certification will be communicated only after an independent audit is completed.
Policies being formalized
Audit logging improvements
SOC 2 readiness work
Independent validation